In October, many security flaws were discovered, and security breaches also occurred. Security researcher Yan Zhu discovered a security loophole in the Android-based platform of the Gmail application.
We all know that phishing is a criminal offense. Still, these researchers have done this pushing. Soon after the security vulnerability was revealed in the Android Gmail app, Yan reported the flaws to the Google Product manager support team.
Bug in Android Gmail App Which Allow Users to Send Hoax Emails
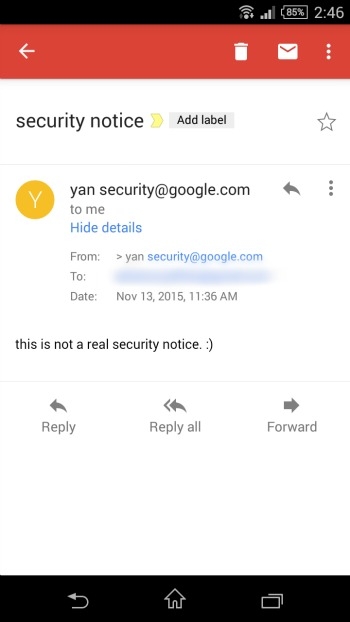
Later on, Yan explained the situation created with the app; here is what happens, the app has some sort of code lack that can allow users to send email to anyone but with a different name; suppose if sender’s name is Mantosh and he can send mail which can show to the receiver as “Mantosh [email protected]” (without quotes) but who it can be shown, the sender can alter the name and email, but email must be having quotes as this “[email protected]” later on to the receiver the quotes will be invisible to the receiver, but the ID as [email protected] will be visible to the viewer with name.
In this case, the sender can hide their real ID with a fake ID to show up to the receiver, which can lead to a big security risk to anyone. With this type of unaware security vulnerability, people may get in trouble, but for a good reason; Yan has told this vulnerability Google, as we have said earlier. But what happened after reporting the vulnerability? The reply from Google security will make you a shock.
filed a gmail android bug that lets me fake sender email address. they said it's not a security issue. ¯_(ツ)_/¯
— yan (@bcrypt) November 11, 2015
The security team replied with a return note to Yan written, “Thanks for your note, we don’t consider this to be a security vulnerability,” soon after the unhealthy response from the Google security team, yan decided to reveal this vulnerability to social networks such as Twitter, as given below.
She said… “Filed a Gmail Android bug that lets me the fake sender email address. They said it’s not a security issue. ¯_(ツ)_/¯”
This can only be done from your Android Gmail application. However, you can also be pressured as a low-risk vulnerability, but, unfortunately, this might still have attracted attention to the culprit or hackers with a dirty mind; this vulnerability can mislead the receiver or the email reader. as I have provided an awesome example above. Only malicious intention has people can do this trick, thanks to Yan Zhu, and all this has been asserted to Google. Still, Google replied with an unexpected answer instead of solving the issue of an Android Gmail application.
Gmail has already developed with spoofed vulnerability possibility; Gmail’s inbuilt features are so strong that they redirect the offended emails to spam or display warning pop-ups to its users.
Motherboard has said about the report, and they have contacted Yan Zhu and Google to discuss the vulnerability. Still, Yan Zhu has already told all this activity to Motherboard. Later on, Motherboard also asked Google to rectify the problems as quickly as possible.
After this situation was created on the Twitter Yan Zhu account, other followers of Yan made fun of her research and her report to the Google Security team. One of the flower Phred had real fun of the tweet, writing, “Send the email from Sergey or Larry and tell them it’s high priority bug that they need to fix immediately, Problem Solved”