As we all know, the Google Play Store is the official app store for the Android OS, allowing users to browse and download applications. Still, from time to time, attackers always try to destroy its security and reputation by spreading their ill-disposed and malicious programs and applications.
Hence, the Antivirus company “Dr. Web” has published another interpretation of the Trojan applications available on the Google Play Store. The malware is distributed under the guise of simple games and service applications and is defined as the “Android.Valeriy.1.origin” by the Antivirus company “Dr. Web”.
“Dr. Web” Detected Another Trojan In Google Play Apps
However, this Trojan is intended to distribute malware,e as we mentioned earlier, which the attackers use to attract users to subscribe to several chargeable services to make money on victims.
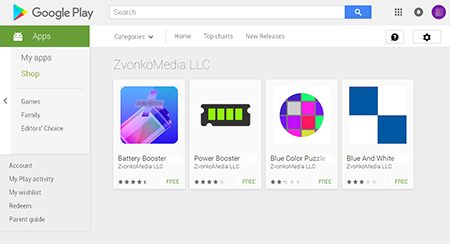
Currently, the following applications on the Google Play Store are from the developers “ZvonkoMedia LLC, Danil Prokhorov and Horshaom” were infected by the Trojan:-
- Battery Booster
- Power Booster
- Blue Color Puzzle
- Blue And White
- Battery Checker
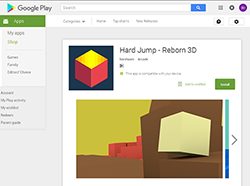
- Hard Jump – Reborn 3D
According to the store statistics, these applications are installed on 15 thousand of units. Once installed on the system, the malware connects to a C&C server and receives a link to a malicious site.
The main goal of the Trojan is to know the victim’s phone number and sign the user on to paid services. Hence, the Trojan can also download and install various applications derived from the C & C JavaScript-script using the WebView server.
As we mentioned earlier that more than 15,500 users have downloaded these applications.
Furthermore, the Antivirus company “Dr. Web” researchers recorded over 55,000 downloads of these applications after they gained access to the Trojan’s C&C server.
Moreover, the Antivirus company “Dr. Web” states, “Our specialists and security experts have already informed the tech giant Google about this occurrence”.