According to the latest reports, due to a severe security flaw, the social network giant Facebook accidentally sends the data in invitations to people who are not friends with the administrator. They can be found in the header of the invitation sent by e-mail. However, now the social network giant Facebook has already closed the gap and paid the researcher a hefty amount of $2,500 as a reward.
This Simple Bug Revealed Admins of Facebook Pages — Find Out How
Security researcher Mohamed Baset has discovered a vulnerability that reveals confidential data of Facebook users. However, only administrators of Facebook pages are affected. Your data will get accidentally sent by the social network giant Facebook via email notifications to users who are not friends with the administrator.
The error that the social network giant Facebook has now removed occurs when a user likes to “Like” a post on a Facebook page but does not follow the page. In this case, the page administrator can invite the user to follow not only the post but also the page by a “Like”.
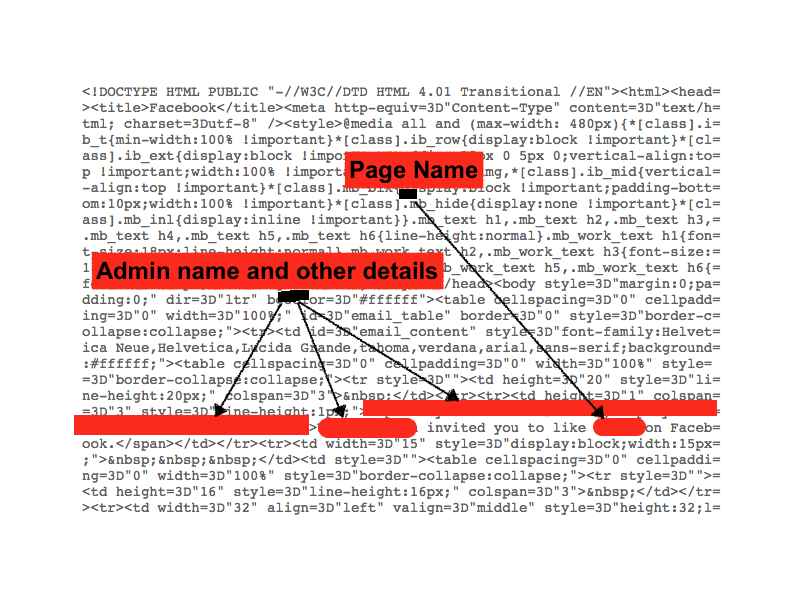
The invitation sent by e-mail attracted the attention of the researcher. Within minutes, he found in the header of the message not only the name of the page in question but also the name of the associated administrator and other personal details. According to his bug timeline, it only took three minutes between receiving the e-mail and sending the bug report to the social network giant Facebook.
“We were able to understand that page invitations sent to non-friends may inadvertently include the name of the page administrator who sent the invitation. We have solved the underlying problem and future emails will not contain this information,” the social network giant Facebook’s response to Baset.
The researcher also rewarded by the social network giant Facebook a hefty amount of $2,500. According to him, it was the second time that he discovered a mistake on Facebook, without having to write a single line of code.
So, what do you think about this? Simply share all your views and thoughts in the comment section below.