Recently a security researcher demonstrated that how your televisions can be easily hacked via Malicious TV Signals and then it can be easily used as a spying weapon by an attacker or any government organization.
90% Of Smart TVs Can Be Hacked Remotely Using Malicious TV Signals
Today, the number and variety of Internet-connected devices (security cameras, Smart TVs and all kinds of smart home appliances) are growing at an exponential rate, and in many cases, they do so in the face of manifestly insufficient security configurations.
However, this type of irresponsible acts inevitably leads to a multiplicity of cyber threats. We all remember the numerous DDoS attacks provoked a few months ago by the Mirai botnet, made up of thousands of IoT ‘zombies’ devices.
Now Rafael Scheel, a cyber security consultant for the Oneconsult firm, has spread another serious vulnerability of the connected devices, in this case Smart TVs. It has done so with a live demonstration during a cybersecurity seminar organized by the European Broadcasting Union (EBU), during which he has made it clear that cybercriminals could take full control of a wide range of smart TVs (almost 90% of those sold in the last years) without having to have physical access to the same terminals: other serious vulnerabilities located in these devices required physical access to them, limiting both the access of hackers and the number of devices potentially affected,
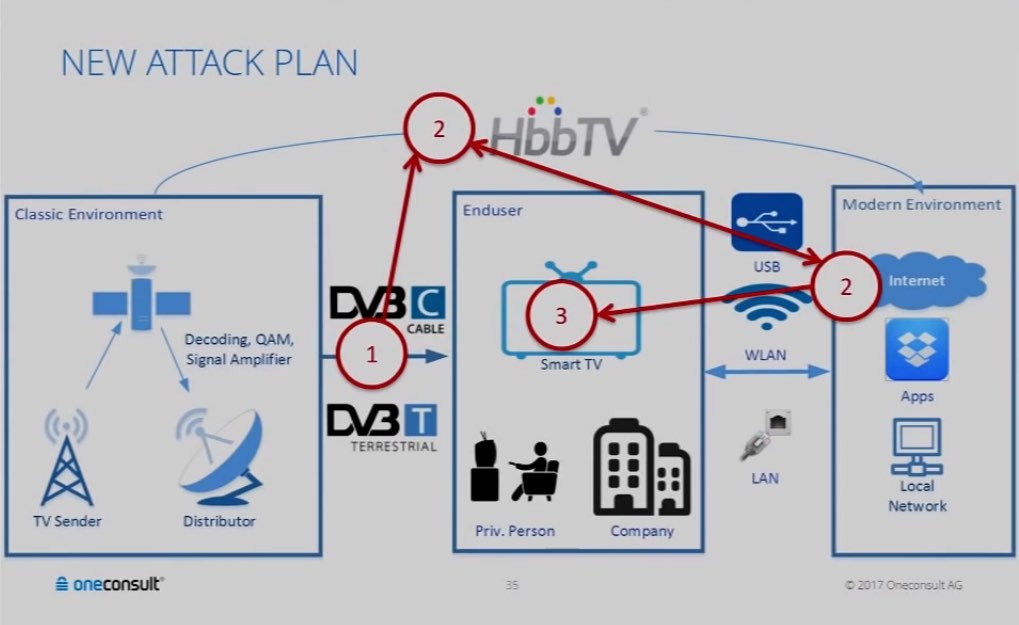
The attack presented by Scheel requires only using a transmitter (affordable for any pocket) that allows to introduce malicious code in DVB-T signals (Digital Video Broadcasting – Terrestrial), a transmission standard present in all terminals with the Internet connection.
From there, it uses two known privilege escalation vulnerabilities, which simply allow attackers to connect to the TV via web interfaces and take full control of the device remotely. And, once compromised, the television can be infected in such a way that no reset or factory reset could repair the Television.