The new information revealed by Wikileaks has shown that How simply using the home Wi-Fi routers the CIA has been able to access all sorts of information over the last few years.
WikiLeaks: CIA Has Tools To Snoop Via Wi-Fi Routers
Recent years have shown that US government agencies, such as the CIA and the NSA, have indiscriminately spied on their citizens and withheld personal information.
The disclosure of these plans has revealed the form used to obtain this information, showing that faults were used in the equipment and software used. The latest information released showed that Wi-Fi routers were also victims and exploited to steal information.
It has been reported that Wikileaks has revealed that cases involving US government agencies have been known. There were several revelations that showed the ways that this agency has used to be able to spy completely anonymously on the American citizens and even of other countries as well.
The new information revealed by Wikileaks has now shown yet another form of this spy agency. Using the home routers, and especially through these Wi-Fi, the CIA has been able to access all sorts of information over the last few years.
In all, and based on the information disclosed, there are 25 types of equipment that are vulnerable to the CIA, from 10 different manufacturers. Despite this information, it is possible that other brands and other models of routers are also vulnerable to this attack.
The list of manufacturers includes the following manufacturers: Apple, Asus, Belkin, Buffalo, Dell, Dlink, Linksys, Motorola, Netgear, Senao and US Robotics. It is not known whether other trademarks have since been added to the list after these documents have been created.
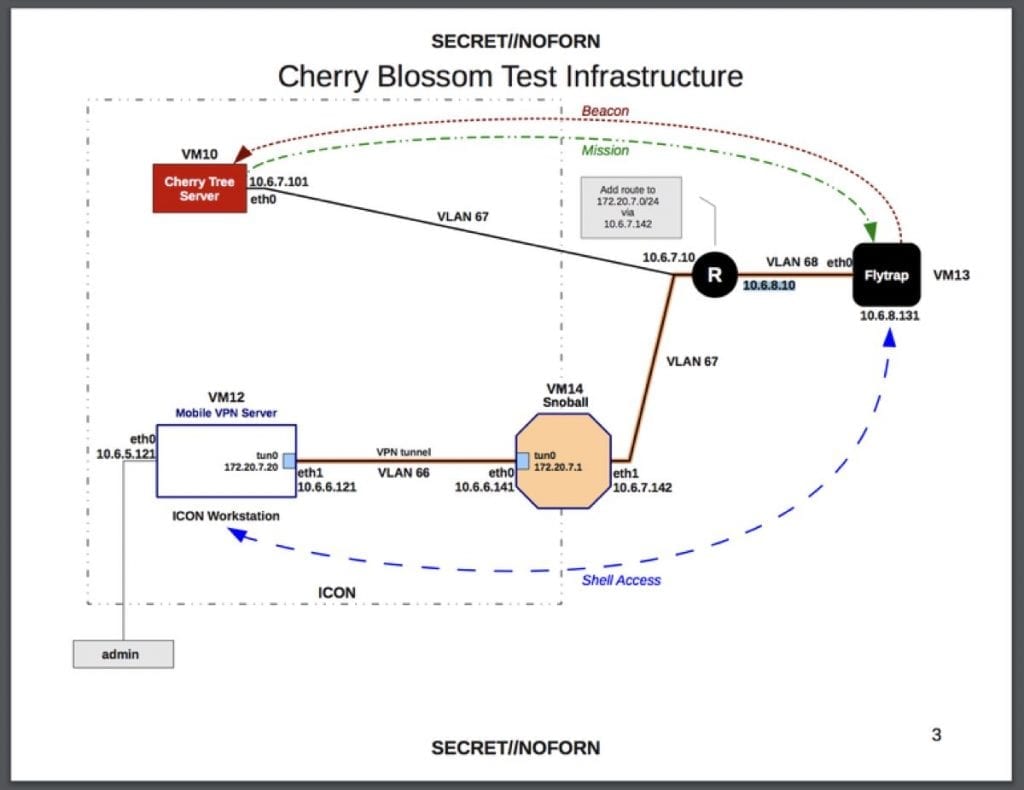
Among the many tools revealed, a special one, CherryBlossom, allows the CIA to monitor the victim’s Internet activity, redirecting the browser and retrieving the information.
Router failures are well known and increasingly simple to exploit, making it one of the preferred targets for these type of attacks. It is not known whether these failures are still being actively exploited or whether the CIA has advanced to new tools. What is known is that updates must be released to correct these faults and they must be applied quickly simply to remain safe.
So, what do you think about this new exploit? Simply share your views and thoughts in the comments section below.