Recently, the tech giant Microsoft has already patched the severe security holes that are actually used by the US national security agency (NSA) simply to spy and hack any PC in the world and access the Information of the citizens.
Microsoft Patched The Security Holes Used By NSA To Spy On Citizens
In recent days a news has spread which is worrying for users of Windows operating systems: the US national security agency would have taken advantage for years of a series of exploits that allowed them to hack any PC in the world and access the Information of the citizens of all poles of the planet.
A group of hackers, self-described as ‘Shadow Brokers’, is the one who has unveiled this alarming practice on the part of the American government. Luckily, the tech giant Microsoft has already patched the security holes related to this threat in Windows 10, among other versions of this operating system.
The vulnerabilities appeared to have been known to the Redmonds for years, although they have publicly stated that no private individual or organization has contacted them to report on these threats. That means, implicitly, that the NSA has not been the one that has alerted of the holes, but that it took advantage with all treachery of the same.
“When a potential vulnerability is reported to Microsoft, either from an internal or external source, the Microsoft Security Response Center (MSRC) initiates an immediate and thorough investigation,” Satya Nadella’s company said in a statement. “Once validated, engineering teams prioritize the solution of the problem as soon as possible, taking into account the time required, as well as the versions affected, the potential threat or the probability of being exploited.”
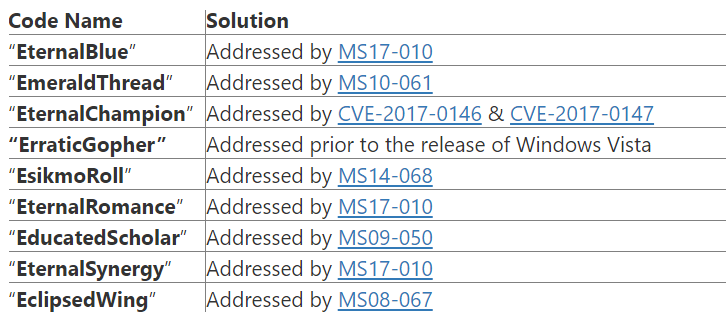
This is the complete list of threats unveiled by the hackers of Shadow Brokers and the corresponding patch provided by Microsoft for its various software:-
The three remaining exploits that have been unveiled, the tech giant Microsoft reports that neither “EnglishmanDentist”, “EsteemAudit” or “ExplodingCan” work on Windows 7, Windows 8 or Windows 10, or Exchange 2010 (onwards).
So, what do you think about this vulnerabilities? Simply share your views and thoughts in the comment section below.