The online black market, which is known as xDedic acting like an eBay for criminals. xDedic has a directory of over 70,000 which is empowering buyers to carry out comprehensive cyber attacks throughout the world.
Site Selling 70K Hacked Government and Corporate Servers for $6 Each
According to the Kaspersky Lab, xDedic simply presents a marketplace for buyers to obtain anything on the web and this time, they have more than 70,000 compromised servers for sale and are being marketed in just $6 a piece.
The servers are from 173 countries belonging to companies, universities, and even government agencies. Thus, other cybercriminals who purchase the database can handle it to access victims more easily, sending spam, stealing data and placing threats to act.
Kaspersky Lab said “The one-time cost gives a malicious buyer access to all the data on the server and the possibility to use this access to launch further attacks. It is a hacker’s dream, simplifying access to victims, making it cheaper and faster, and opening up new possibilities for both cybercriminals and advanced threat actors.”
According to the sources, Kaspersky Lab teamed up with Europen ISP and discovered that xDedic is a marketplace that might have been created by Russian speakers. The number of compromised servers in March 2016 was 55,000 and in May 2016 it is 70,624. That means it became a marketplace where a network of affiliates can trade compromised servers.
xDedic used to connect sellers of compromised servers with illegal buyers, and xDedic takes 5 percent up-front payment of all money put into trading, said Costin Raiu, director of Kaspersky research and analysis team.
Chart below will show you the location of the hacked servers
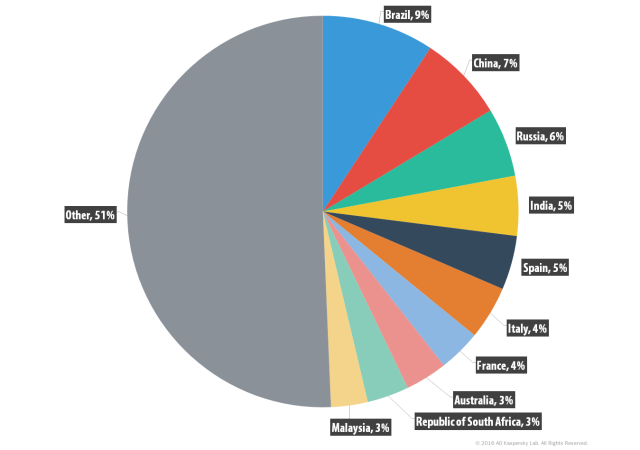
The chart is being flourished for almost two years and has more than 416 sellers now. According to the chart listed above, we can see Brazil sharing nine percent of hacked server, China 7%, Russia 6% etc.
Kaspersky Labs said “We were able to identify some high profile victims such as Governmental entities and universities.During the investigation, we worked with several partners which allowed us to notify some of the victims about the infections in their networks.”


