There are seven types of hackers some of them motivate others to become good hackers as White Hat Hackers and others motivate to become worse as we say Black Hat Hackers.
In the world, there are seven types of hackers some of them motivate others to become good hackers as White Hat Hacker and others motivated to become worse as we say Black Hat Hackers. These two hackers are at the topmost hackers in the list, but rest includes Script Kiddies, Hacktivists, State-Sponsored Hackers, Spy Hackers and Cyber Terrorist.
And the topic is Black Hat Hackers who basically comes under the list of criminals, this hacker violates computer system programs for some reason and mainly for personal gain, illegal activity within the cyber web calls off about cybercriminals and thus Black Hat hackers does this by inserting the malicious content to another computer. There are no exact terms may be they are in a group or an individual working in the field of illegal hacking again for personal gain.
Top 10 Black Hat Hackers Who Made History Forever
Black Hat Hackers hack into the SSL or secure web servers or any computer to steal or destroy data and they can also make the computer network unusable, A black-hat hackers basically breach into the network system and get it compromises without the prior knowledge of the victim, this hackers get infringement access to the system or a giant network to accompany the technological advancement of the computer overall connected networks. Below we have Top 10 Black Hat Hackers who have made history for all seven hackers, might be called a personal experience of those black hat hackers.
Also Read: Best Website To Learn Ethical Hacking
10. Albert Gonzalez
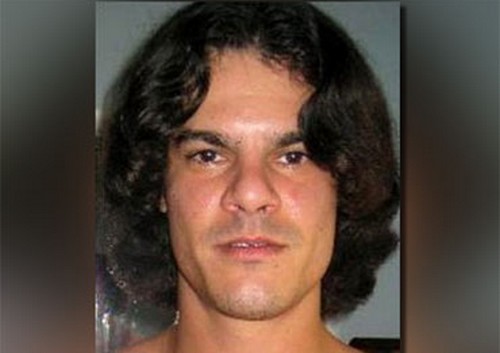
Albert Gonzalez is a well-known hacker as well as a cybercriminal, with his own team he became the mastermind in stealing of more than 170 million credit cards and ATM details between 2005 to 2007 in which it claims the biggest claim in history. The techniques Gonzalez team using at that time seems authentical SQL injection techniques in which it generates the malware backdoor on several computer systems, the office computer, home computers and mainly targeted corporates offices networks in order to launch packet-sniffing or ARP spoofing attacks into all those systems and networks to steal internal computer valuable information which worths in millions, later he was arrested on March 25, 2010 – with his team and seized $1.6 million in cash including $1.1 million found in a plastic bags stored in a drum which was buried in his parents backyard, he was sentenced for 20 years.
9. Vladimir Levin
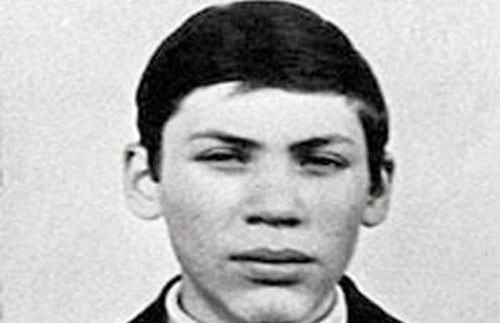
Vladimir Levin mainly becomes popular after he transfer US$10.7 million from Citibank’s computer network, he is a Russian-born belongs to Jewish family, Vladimir Levin lived a short life as a hacker because later on after stealing $10.7 million from bank he was arrested and the authority able to recover all only $6.7 million and the rest $400,000 has no record.
After his release he went to the United States in his trial he was told to coordinate the first internet banking raid. Later on, he committed his ability to transfer Citibank customer funds to his own account which is through stealing the account numbers and PINs.
8. Kevin Poulsen

The more we go to the nearest numbers the more the 80s and 90s hackers will be revealed. Kevin Poulsen ’80s black hat hacker who hacked into the Los Angeles Radio KIIS-FM phone line which made him rich in one day to purchase a brand new Porsche, The law enforcement dubbed him “the Hannibal Lecter of computer crime.”
Kevin Poulsen didn’t stop here, he then hacked into a federal investigation database. He mention rage during the hacking pursuit into the FBI federal computers to wiretap information, he usually became more famous in hacking telephone lines and connection criteria, later on when his photo shown in Unsolved Mysteries at that time he crashed 1800 telephone connection lines and at last he was captured in a supermarket and he was sentenced for five years, after serving five years in jail he moved on a right path and now he is a senior editor in Wired News.
Also Read: Whatsapp Tricks and Whatsapp Hacks
7. Robert Tappan Morris

In our number 7th Mr Morris who become popular in 1988 after creating a computer worm which was considered to be the first computer virus he had created. Robert Tappan Morris is known as an American computer scientist in 1986. Not only he created the first computer virus but also being arrested in 1990 under the Computer Fraud and Abuse Act. Previously he has been a student when he created that Morris virus while studying at Cornell University, he spread that Morris virus all over the internet which affects 6,000+ computers.
After this computer fraud, he serves sentence for three years in federal jail for probation, Morris capture because of his own fault, before creating the Morris virus he gradually chatting with his friends and knowing ones about who he is creating this virus and that faced him jailed otherwise he has used his college name, Cornell, he said would have said that the virus is originally originated from his college Cornell and he flew away from the case.
6. Michael Calce
Michael Calce is a high school boy basically best known as ‘MafiaBoy’ from West Island also he himself moniker as Michael Demon Calce. he is the first person who launched DDoS which in terms Distributed Denial of Service attacks against a large number of multination companies websites and online services, firstly includes Yahoo!, Amazon.com, Dell, CNN and eBay. All this site already being affected but in terms of Yahoo! at that time it was the leading search engine who stopped working for one hour after the DDoS attack by ‘MafiaBoy”, Later on, Calle arrested for serving Eight months in custody and one year of probation.
5. Kevin Mitnick

A boy calls himself as a hacker moniker “Hacker Posted Boy” Mitnick experienced an exceptionally pitched interest by powers. His wickedness was built up by the media however his real offences may be less remarkable than his reputation recommends. He broke into DEC’s PC arrange and duplicated their product, wrongdoing he was accused of and sentenced in 1988.
4. George Hotz

He Calls as George Francis Hotz also Geohot, he is an American hacker basically capable of unlocking iPhone devices, the hacking into the phone controls from another wireless device, just irreconcilable of AT&T and Apple. the most important is he developed Limera1n jailbreaking tool and bottom to exploit iOS.
Gotz becomes the first person in 2007 to unlock iPhone devices, in his blog www.geohot.com he claims he had traded his second unlocked 8 G iPhone to the founder of Certicell Terry Daidone in which in return he got Nissan 350Z and three 8 GB iPhones. in 2010 he publically declares about his discontinuation in Jailbreaking activities also declare about his demotivation over hacking techniques and now wanted to get unwanted personal attention, now he is a software developer working with Sony Playstation.
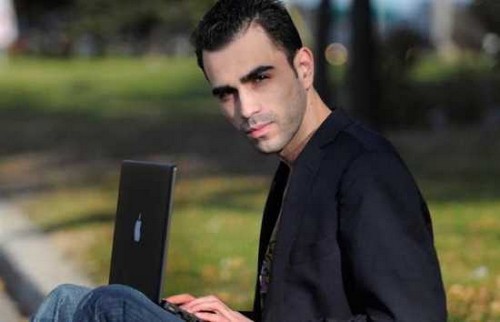
3. Adrian Lamo

Adrian Lamo is a Colombian-American risk investigator and program. He utilized coffeehouses, libraries, and web bistros as his areas for hacking.
Aside from being the destitute program, Lamo is generally known for breaking into a progression of prominent PC systems, which incorporate The New York Times, Microsoft, Yahoo!, and MCI WorldCom. In 2002, he added his name to The New York Times’ inward database of master sources and used LexisNexis record to direct research on prominent subjects.
2. Gary McKinnon

A real black hat hacker Gary McKinnon, In 2002, an extraordinarily odd message showed up on a US Army PC screen: “Your security framework is poor,” it read. “I am Solo. I will keep on disturbing at the most elevated amounts.” It was later distinguished as the work of Scottish frameworks executive, Gary McKinnon, who was blamed for executing the “greatest military PC hack ever”. He is blamed for hacking into 97 United States military and NASA PCs over a 13-month period between, utilizing the name ‘Solo’.
The US powers claim he erased basic documents from working frameworks, which close down the United States Army’s Military District of Washington system of 2,000 PCs for 24 hours. In November 2002, McKinnon was arraigned by a government amazing jury in the Eastern District of Virginia.
After the September 11 assaults in 2001, he erased weapons logs at the Earle Naval Weapons Station, rendering its system of 300 PCs inoperable and deadening weapons supply conveyances for the US Navy’s Atlantic Fleet. He is likewise blamed for replicating information, record documents, and passwords onto his own PC.
The arraignment contained seven numbers of PC related wrongdoing, each of which conveyed a potential ten-year correctional facility sentence. The court had prescribed that McKinnon is secured to the United States to face charges of illicitly getting to 97 PCs, bringing about an aggregate of $700,000 in harm.
1. Jonathan James
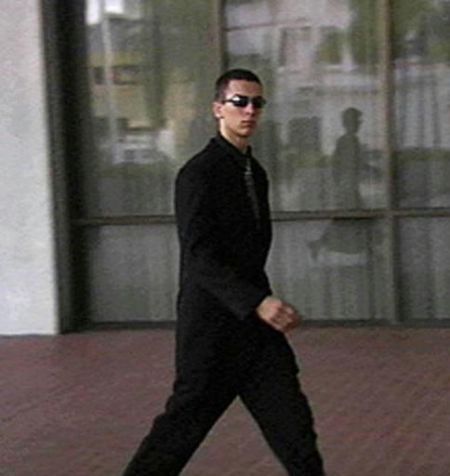
A 16-year-old dark cap programmer Jonathan James turned into the first adolescent detained for cybercrime. James picked up his reputation by actualizing a progression of effective interruptions into different frameworks. In a mysterious PBS meeting, he proclaims, “I was simply glancing around, playing around. What was a good time for me was a test to see what I could draw off.”
James’ real interruptions focused on prominent associations, for example, NASA and the Department of Defense. He broke into NASA PCs, taking programming worth around $1.7 million. He likewise hacked into the Defense Threat Reduction Agency and caught more than 3,000 exceptionally hidden messages going to and from the DTRA representatives while gathering numerous usernames and passwords.
James conferred suicide utilizing a weapon, On May 18, 2008, at 25 years old. His suicide was obviously spurred by the conviction that he would be indicted for violations he had not submitted. “I truly sincerely had nothing to do with TJX,” James wrote in his suicide note, “I have no confidence in the “equity” framework. Maybe my activities today, and this letter will send a more grounded message to the general population. In any case, I have lost control over this circumstance, and this is my best way to recapture control.”