We will talk about the significant computer issue named Trojan horse Virus. Trojan horse virus is one of the critical types of viruses that can affect your computer a lot. Go to the full post to learn about it and how to get rid of it.
Today we came up with the influential computer problem, What is the Trojan horse virus and how to Remove it? Viruses can access our computers in many ways, like through Internet Browsing, USB devices, and by installing some infected software.
Also Read: How To Remove Computer Viruses Using CMD
These viruses cause our computers to run slowly, and some dangerous viruses hijack our data. These viruses can also corrupt our operating systems. And the Trojan horse virus is one of the critical types of viruses that can affect your computer significantly.
This virus can access your files and multiplies itself too. Just read out the below to have complete information on this.
What is the Trojan horse virus, and how to Remove it?
Suppose a virus creates a text editor file that is used to access the location of other files and put them in a particular area that can be editable by that text editor file. In that case, the file is a trojan horse file designed to modify the user data without any authentication. Also, another variant of the trojan horse is spyware; this spyware generally comes with freeware software, gets installed on your operating system, and sends your personal identification information to the spying computer.
BullGuard security says that Trojan Horses make up more than 70 Percent of computer-detected malware. Users might encounter unrequested Web pages appearing in their browser.
MacAfee Security advice center says that most Trojans are delivered via emails, online services, and downloads such as free apps, Games, movies, etc. Trojan Horses can initiate harmless pranks and display cute, obscene, or political messages.
Trojan Horses can erase all your data and can even try to damage your hardware components. Hackers can track your keystrokes and collect them from your computer without your knowledge.
Also Read: How To Check Whether Your Antivirus Working Perfectly Or Not
Remove Trojan Horse Virus
Just follow the steps below to remove the trojan horse from your computer.
Never Open Suspicious Files in Emails
First, you need to beware of “executable” file attachments. You might receive files extension such as .vbs, .exe, .bat etc. You might even receive files that have multiple extensions like “Job-letter-text. VBS”. Be careful while handling this type of extension. In the end, That’s the only one that counts.
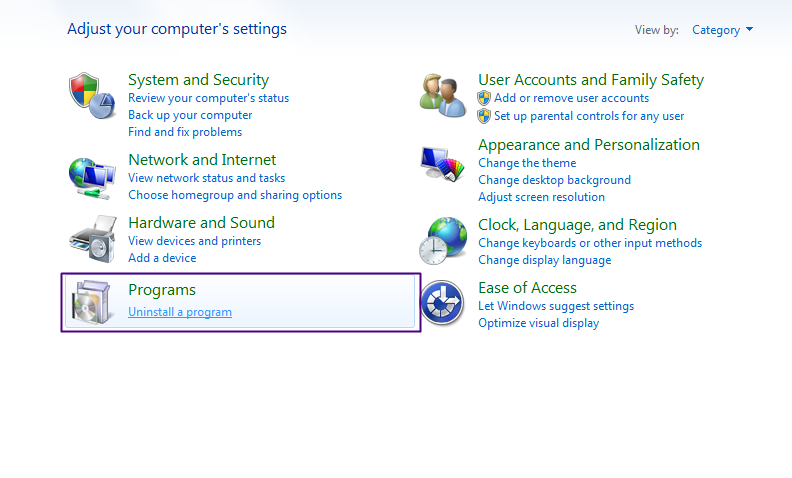
Uninstall The Unsafe Programs
First, you need to find any of the software you’ve not installed, which might be automatically installed on your computer; for that, go to Control Panel->Uninstall a Program. Now there, have a look at all the programs and uninstall the program you’ve not installed by you on your computer.
Also Read: How To Scan Files & URLs Without Any Antivirus Installed
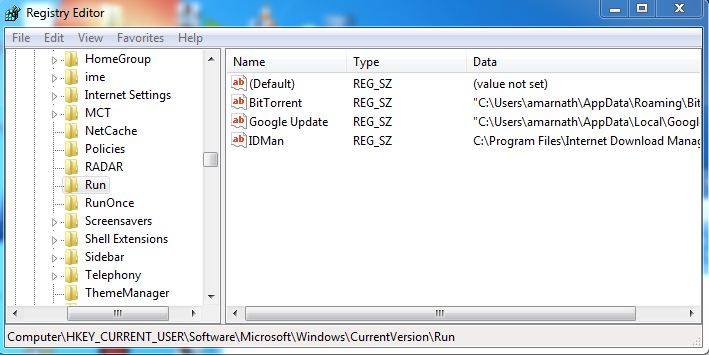
Registry Edit
Press Winkey and R simultaneously, type in regedit, click HKEY_CURRENT_USER, Software, Microsoft, Windows, CurrentVersion, Run, and there, look at the program that you might not know that you have installed. Now look for the suspect software and search it on Google; it will tell you everything about that program. And if it is trojan, then uninstall that.
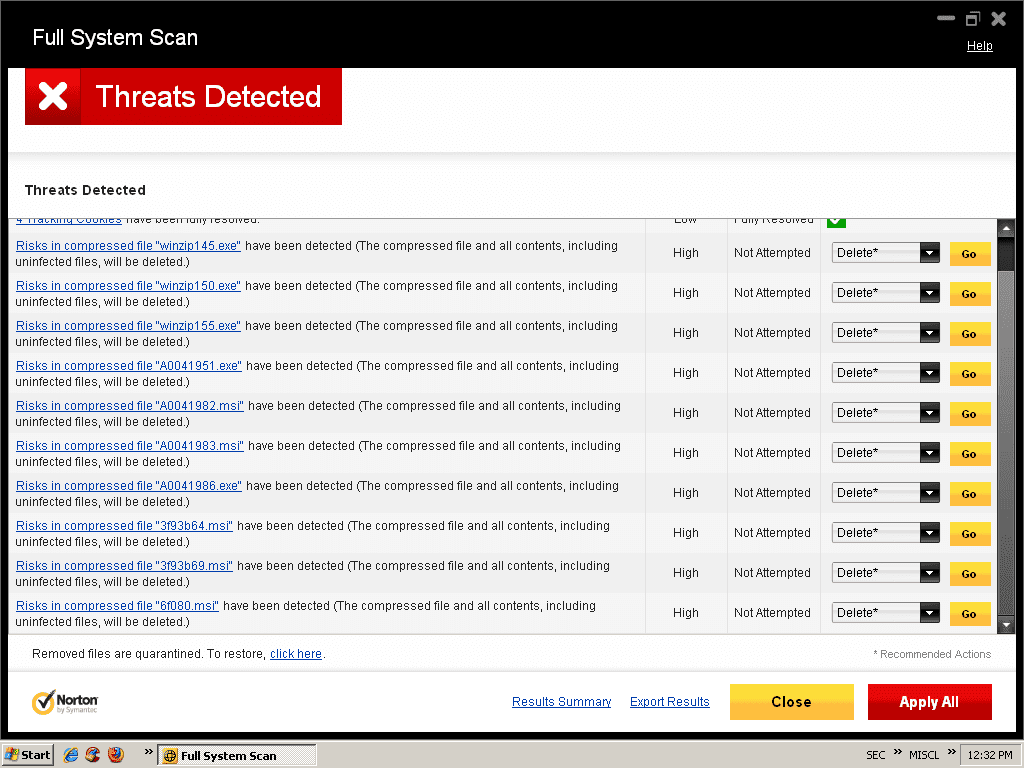
Scan Through Your Updated Antivirus or Antimalware
You can also remove this trojan automatically using anti-malware and anti-spyware; if you don’t have one, you can download one online.
Also Read: 6 Signs That Your PC is Infected with a Virus or Any Malware Installed
Scan In Safe Mode
This is a must-do process to get rid of Trojan horse Viruses. You need to log in to your system in Safe Mode. You have to select Safe mode with networking, and you need to perform a full scan in Safe mode. You can get into safe mode repeatedly pressing the F8 button while your computer starts.
By taking care of all these steps, you can quickly eliminate the trojan horse virus from your computer.
Also Read: How To Remove All Viruses From PC Using Rescue USB Disk
Use Hitman Pro
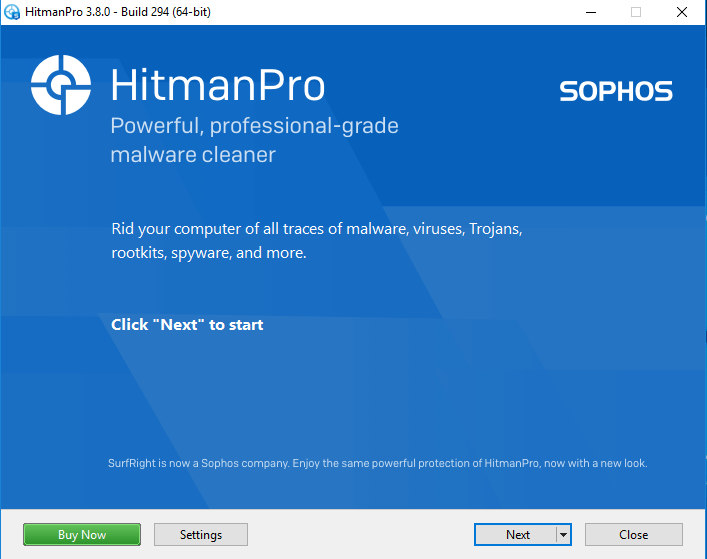
HitMan Pro is the best and most powerful malware removal tool on the web. The great thing about Hitman Pro is that it effectively scans and removes malware, virus, Trojans, rootkits, spyware, etc. So, here’s how you can use HitMan Pro to Remove Trojan Horse
1. First of all, visit Hitman Pro’s webpage from the computer and download it on your computer. This is a premium app that offers 30 days of a free trial. You can opt for the free trial first.
2. Now run the Hitman Pro’s installer on your windows computer. Now open the app and click on ‘Next.
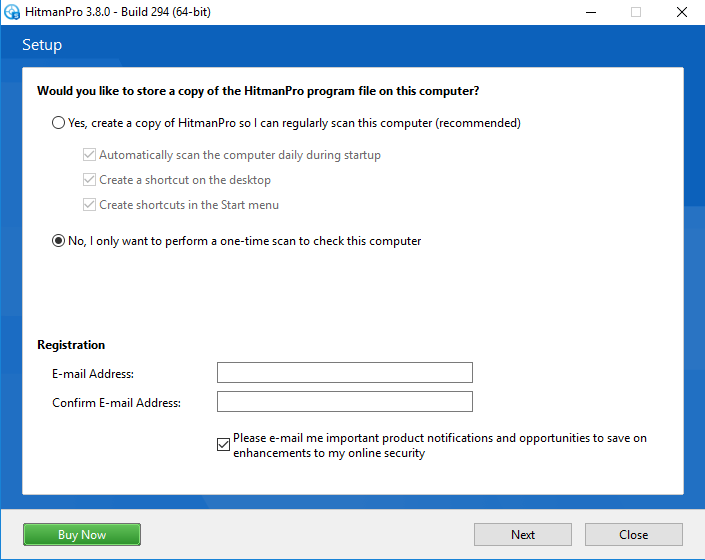
3. In the next window, you must select ‘No, I only want to perform a one-time scan..’ then click Next.
4. Now, Hitman Pro will scan your computer for malicious content. It will find and remove all trojans, rootkits, bad registries, malware, virus, etc.
HitMan pro sometimes detects important .dll files or other things as malware. So, this is how you can use Hitman Pro to remove Trojan horse from your computer. Make sure to double-check the files before deleting them.
So, above is all about What is Trojan horse virus and how to remove it. By these steps presented above, you can easily remove these infected files and spyware from your computer and can guarantee your security and secure your data from being contaminated by these. Hope you like our post, and don’t forget to share this excellent method with your loving ones to aware them about this computer threat. And leave a comment if you are facing any trouble.