Your computer device makes connections to outside sources whenever you connect to the internet. These connections are safe when they are under your control. But there can be some connections that can be made without your consent.
You may notice such connections when any of your apps silently tries to connect to the internet. Malicious apps can sit on your system without being detected for months, and such apps try to grab data from your computer and send it to its server.
Steps to Uncover Unauthorized Connections in Windows
You can easily find such apps by checking all unauthorized connections Windows makes. Below, we have shared some simple steps to show you all the unauthorized connections your PC is making. Let’s check out.
Through Using PowerShell
In this, you will be using an inbuilt feature of Windows to access PowerShell and see hidden connections activity.
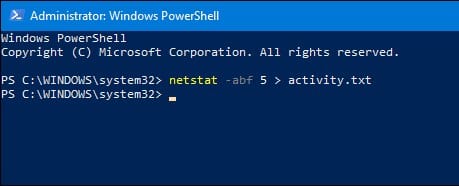
1. First, click on the Windows search and type PowerShell. Right-click on PowerShell and select ‘Run as administrator‘.
2. When the PowerShell starts, execute the command:
netstat - abf 5 > activity.txt
3. Now your PC will begin recording the associations being made and spare them to a content document. Let the program run for a few minutes.
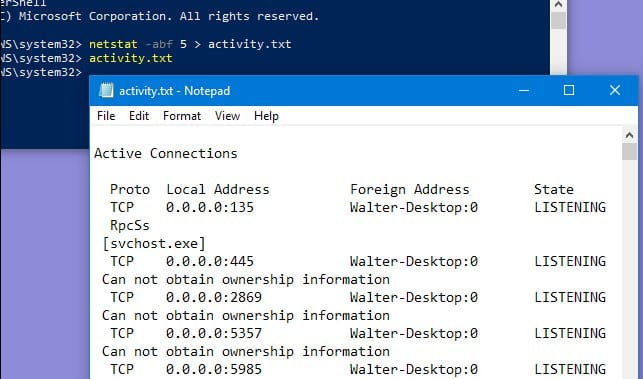
4. Once done, type “activity.txt” and press Enter to see the data the program recorded.
5. Finally, open the .txt record in Notepad.
Now you will see all connections made from your PC. If you suspect something suspicious, you need to search for it on the internet.
So, these are some simple steps to uncover unauthorized connections your Windows computer is making. The method we have shared requires no third-party app installation. Hence it’s completely safe to use.