If you are an iTunes user, you may know that the service has an authorization system that ensures that your computers can access all your purchased videos, music, etc.
Once you authorize your Mac or PC, you are giving that device permission to access all books, music, movies, audiobooks, etc., stored on your iTunes.
While it’s an interesting feature, if you plan to sell your computer, you may want to deauthorize it on iTunes.
Steps to De-Authorize A Computer from iTunes
So, removing or deauthorizing your computer from iTunes is best if you are about to trade away your Mac or PC. Below are some of the easy steps that will let you do so.
1. The first step is to open iTunes on any computer device and click on the Accounts settings. Inside the Accounts settings options list, you have to click on Authorizations.
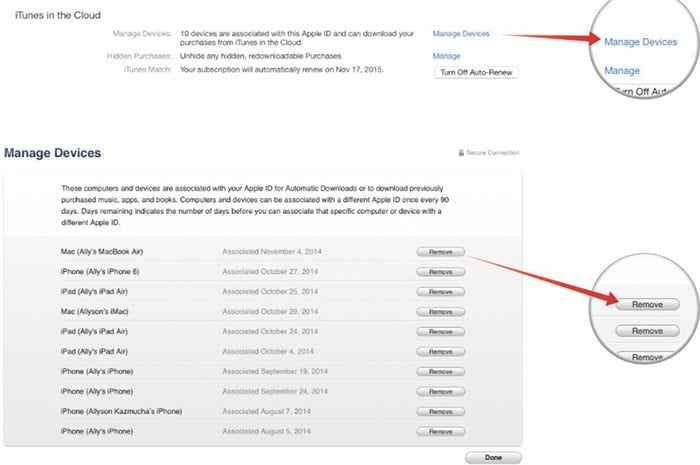
2. This Authorizations option would link to the page that shows all the computers or devices authorized with your device or account.
3. In the above step, you will be prompted by the panel asking for the Apple ID and password. Just fill in the same for your account for which you need to make the amendments.
4. Click the deauthorize button on the other prompt to ask permission to remove any of your selected devices from the authorization list.
That’s it! This is how you can de-authorize a computer from iTunes.
So, these are some of the easy steps to de-authorize a computer from iTunes. If you need more help de-authorizing computers from iTunes, let us know in the comments below. Also, if the article helped you! Please share it with your friends as well.